Real-Time Ransomware & Data-Leak Monitoring
Detect extortion threats, stolen data, and brand exposure before attackers escalate - with verified intelligence you can act on.
- Live monitoring of ransomware and extortion ecosystems
- Early alerts before public data leaks
- Dashboard, email, and API delivery
- One-of-a-kind leaked file name search
- Trusted by security teams at Fortune 100 companies, global operating law firms, and leading DFIR teams
No spam. We’ll show you the platform and a sample report for your sector.
Protect Your Data.
Early warning, actionable context, and operational delivery - built for security teams. Get notified when your third-parties and customers are targeted.
Early warning
Detect new leak claims and extortion activity as it happens.
Actionable context
Enriched details: entity mapping, artifacts, links, timeline.
Operational delivery
Alerts + dashboard + API to automate workflows and reporting.
Built for Risk Teams, Compliance, SOC, DFIR
- and Your CISO.
A simple workflow: collect signals, enrich context, alert quickly, deliver outputs.
Ransomware & Data-Leak Trends Security Teams Must Track
Ransomware in 2026 is no longer just about encryption - it is driven by data theft, extortion, and public exposure. Attackers increasingly pressure organizations by leaking stolen data on dedicated extortion sites, social channels, and underground forums.
Extortion-first attacks are now the norm
Many campaigns skip encryption entirely, focusing on data theft and public shaming to force payment.
Leak sites act as early breach indicators
Victim listings often appear days or weeks before incidents are publicly disclosed or detected internally.
Attackers target reputation and trust
Stolen data is selectively leaked to maximize regulatory, legal, and brand impact.
Ransomware ecosystems are fragmented and fast-moving
Groups rebrand, splinter, and migrate infrastructure to evade takedowns and monitoring.
Manual monitoring no longer scales
Hundreds of active extortion sources make human-only tracking unreliable and slow.
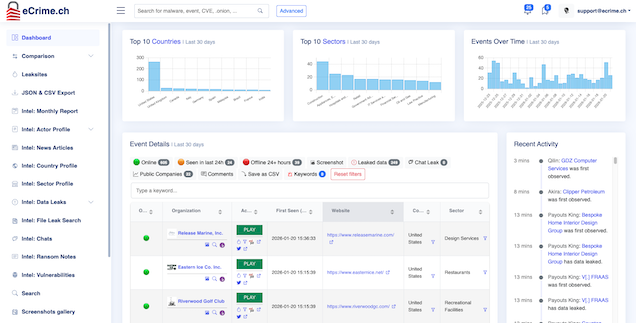
Live Monitoring Output
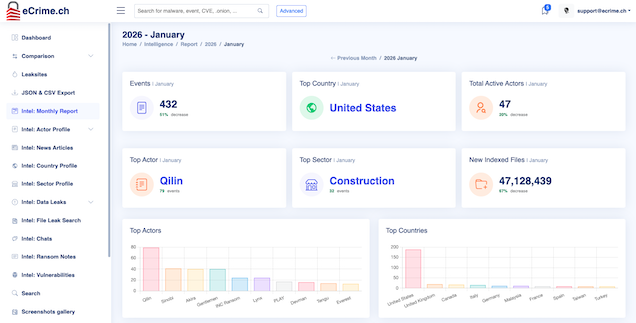
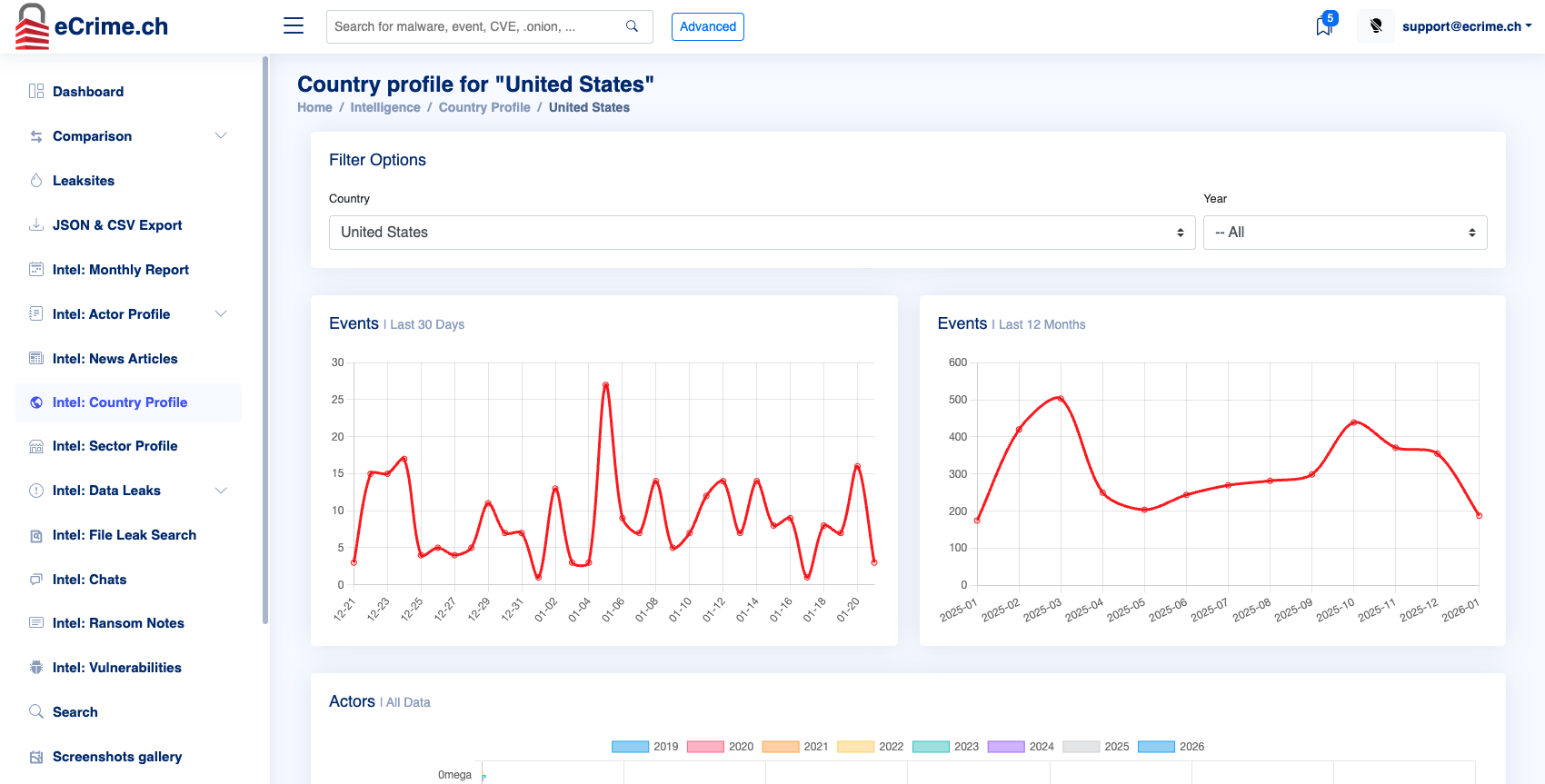
Real-time ransomware and data-leak monitoring metrics.
These numbers reflect automated detection plus analyst validation, and are updated regularly.
Alerts issued (30d)
—
New claim listings (30d)
—
Sources monitored (30d)
—
Avg alert latency
—
Trend: New Claim Listings (Last 30 Days)
Last 7 Days Snapshot
| Date | New claims | Data Leaks | Screenshots |
|---|
What You Actually Get
The eCrime.ch platform provides real, actionable insights with examples of dashboards, alerts, reports, and API outputs. Explore how our tools can help your team stay ahead of threats and make informed decisions.
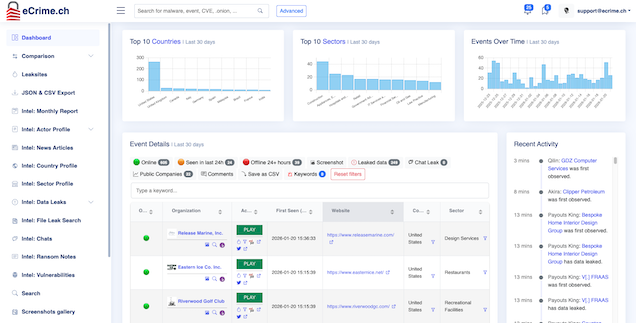
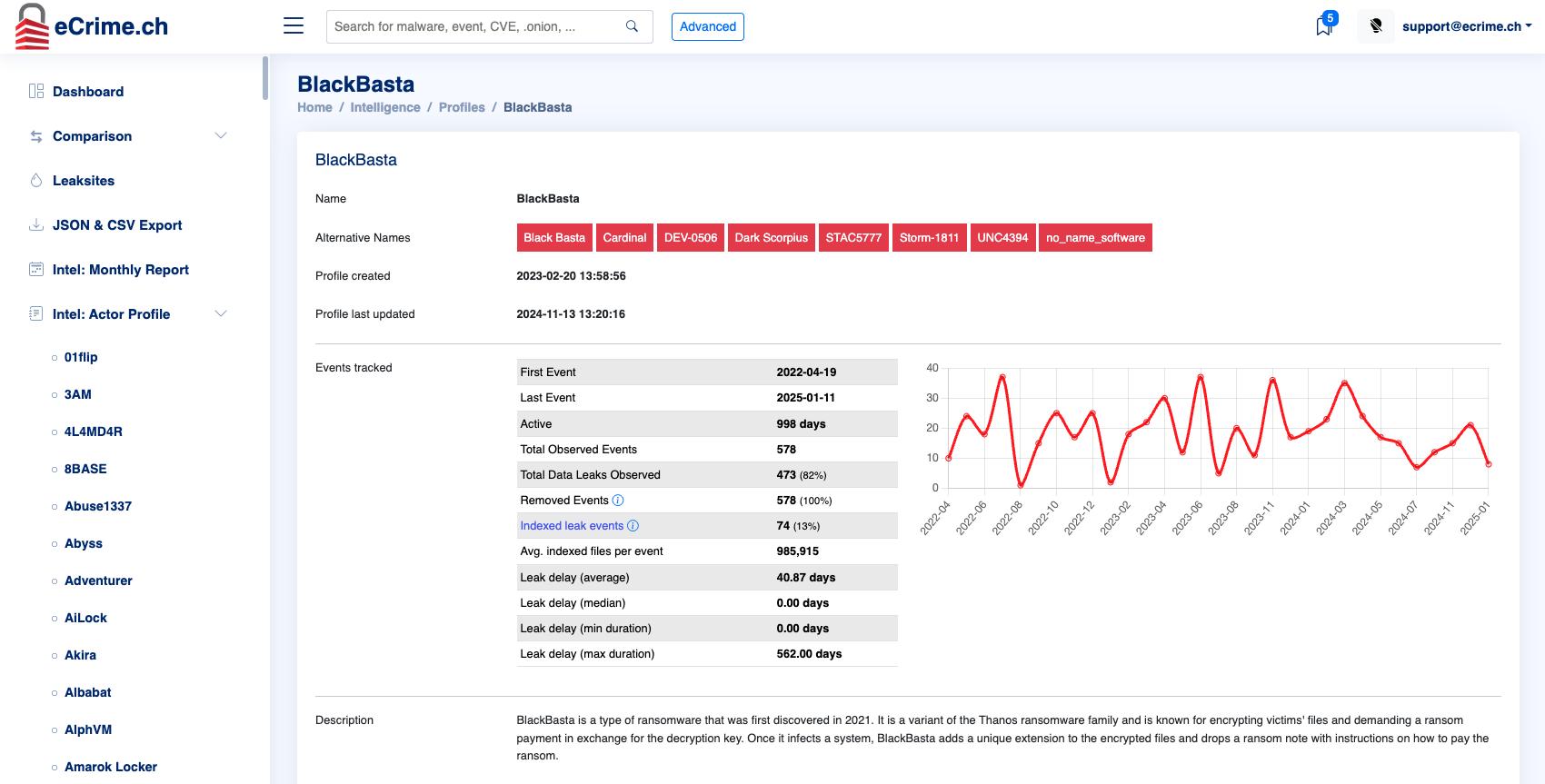
Dashboard
Search, filter, and review cases with context your team can act on.
- Case view with timeline and artifacts
- Tags, notes, export
- Collaboration-ready links
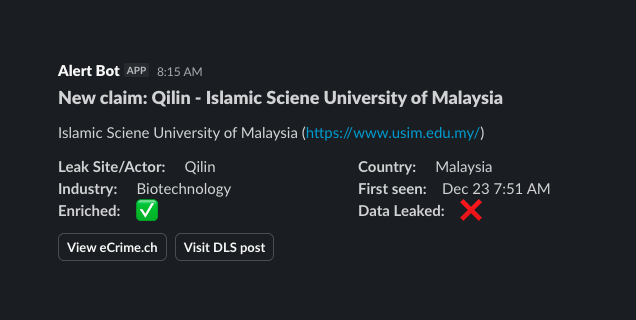
Real-time alerts
Get notified immediately when an entity you care about appears in relevant activity.
- Keyword / domain / entity watchlists
- Sector filters and priority scoring
- Email, Slack, and webhook delivery
Reports
Executive-ready summaries your stakeholders will actually read.
- Weekly digest & monthly brief
- Custom reports for portfolio / vendors
- PDF/Slides-ready output
API
Integrate with SIEM/SOAR, case management, or internal tooling.
- Entity & case endpoints
- Webhook delivery
- Export and automation workflows
curl -sS "https://ecrime.ch/api/v1/events/search/ExampleCo/" \
-H "X-API-Key: YOUR_API_KEY" \
-H "Accept: application/json"
# Example response (truncated)
{
"data": [
{
"id": "42",
"first_seen": "2023-07-09 05:31:14",
"last_seen": "2023-07-09 14:16:34",
"leak_site": "8BASE",
"leak_title": "ExampleCo",
"country": "Canada",
"sector": "Oil and Gas",
"name": "Example Co., Inc.",
"website": "https:\/\/www.example.com\/",
"employees": "11-50 employees",
"leak_url": "http:\/\/basemm....onion\/company\/123456",
"duplicate": null,
"data_leak": 0,
"last_update": "2023-07-09 05:32:34",
"extra": "REMOVED<\/div>",
"logo": "https:\/\/ecrime.ch\/image\/logos\/logo.jpg",
"keyword": "false"
}
]
}
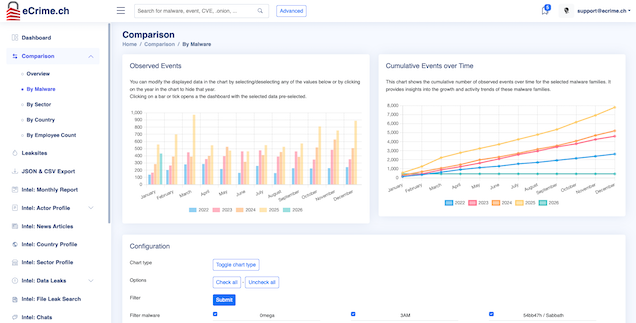
Comparison
Executive-ready summaries your stakeholders will actually read.
- Weekly digest & monthly brief
- Custom reports for portfolio / vendors
- PDF/Slides-ready output
File Search - Try It!
Curious what files are leaked? Try our file search tool.
Enter any file name below to see if it has been exposed. The search will return up to 10 results.
Use eCrime.ch To …
Empower your team with actionable insights tailored to your unique security challenges and mitigate third-party risks by continuously monitoring your vendors and critical suppliers for potential exposure.
Incident response
Confirm claims, track updates, brief leadership with facts.
SOC monitoring
Alerting + automation via API, aligned to your workflows.
Third-party risk
Monitor vendors and critical suppliers continuously.
Brand protection
Track extortion threats and related abuse signals.
Insurance / underwriting
Signals that help inform exposure and monitoring posture.
Executive reporting
Weekly/monthly summaries that drive decisions.
Why Teams Choose eCrime.ch
Stay ahead and improve your teams work - trusted by organizations to deliver precise, real-time intelligence that protects your business and reputation.
| eCrime.ch | Generic feeds | |
|---|---|---|
| Strong leak-ecosystem focus | ✅ | ⚠️ |
| Entity matching | ✅ | ✅ |
| Alerts + dashboard | ✅ | ✅ |
| API + automation | ✅ | ⚠️ |
| File name search | ✅ | ❌ |
| CAPTCHA bypasses | ✅ | ❌ |
| Zapier App | ✅ | ❌ |
| Integrate into existing business processes | ✅ | ⚠️ |
Simple Plans for Teams of Any Size
No complicated pricing or hidden fees.
Professional
Most popular- One (1) account included
- Claims screenshots
- Dashboard & API access
- Email alerts (keyword, daily, weekly)
- Full data exports
- File name search
Commercial
- Ten (10) accounts included
- Everything in Professional
- Commercial re-use of data
- Entity watchlist
- Full data exports
- Integration support
Enterprise
- Custom account count
- Everything in Professional
- Self-service portal for account management
- SLA & priority support
- Shared keyword watchlists
- SSO integration
Frequently Asked Questions
Address common questions and concerns to help clarify coverage, accuracy, legality, support, and data integration.
Built in Switzerland. Trusted Globally.
We take data privacy and compliance seriously.
Swiss-based operations
Our service is proudly Swiss, with all operations and data storage based in Switzerland. Our team consists of Swiss professionals dedicated to ensuring the highest standards of quality, privacy, and security.
GDPR-aware data handling
We ensure secure data storage of customer data in Switzerland and Europe, adhering to the highest standards of privacy and compliance for all clients.
Clear privacy and legal disclosures
Ensure transparency and trust with our commitment to clear privacy and legal disclosures. We prioritize compliance and data protection, providing you with the confidence to operate securely in a rapidly evolving digital landscape.
Get Ahead of Ransomware and Leak Claims.
Tell us what you want to monitor. We’ll show you the dashboard and a sample report for your sector.